
CBSE Class 12 Computer Science Marking Scheme (2020-21)
- Categories Sample Papers
Class: XII Session: 2020-21
Computer Science (083)
Sample Question Paper (Theory)
Maximum Marks: 70 Time Allowed: 3 hours
General Instructions:
1. This question paper contains two parts A and B. Each part is compulsory.
2. Both Part A and Part B have choices.
3. Part-A has 2 sections:
a. Section – I is short answer questions, to be answered in one word or one line.
b. Section – II has two case studies questions. Each case study has 4 case-based subparts. An examinee is to attempt any 4 out of the 5 subparts.
4. Part – B is Descriptive Paper.
5. Part- B has three sections
a. Section-I is short answer questions of 2 marks each in which two question have internal options.
b. Section-II is long answer questions of 3 marks each in which two questions have internal options.
c. Section-III is very long answer questions of 5 marks each in which one question has internal option.
6. All programming questions are to be answered using Python Language only
Part-A
Section-I
Select the most appropriate option out of the options given for each
question. Attempt any 15 questions from question no 1 to 21.
1 . Find the invalid identifier from the following
a) MyName
b) True
c) 2ndName
d) My_Name
Ans. b) True
2. Given the lists L=[1,3,6,82,5,7,11,92] , write the output of print(L[2:5])
Ans. [6,82,5]
3 . Write the full form of CSV.
Ans. Comma Separated Value
4 . Identify the valid arithmetic operator in Python from the following.
a) ?
b) <
c) **
d) and
Ans. c) **
5 . Suppose a tuple T is declared as T = (10, 12, 43, 39), which of the following is incorrect?
a) print(T[1])
b) T[2] = -29
c) print(max(T))
d) print(len(T))
Ans. b) T[2]= -29 (as tuple is immutable)
6 . Write a statement in Python to declare a dictionary whose keys are 1, 2, 3 and values are Monday, Tuesday and Wednesday respectively.
Ans. Day={1:’monday’,2:’tuesday’,3:’wednesday’}
7 . A tuple is declared as
T = (2,5,6,9,8)
What will be the value of sum(T)?
Ans. 30
8 . Name the built-in mathematical function / method that is used to return an absolute value of a number.
Ans. abs()
9 . Name the protocol that is used to send emails.
Ans. SMTP
10 . Your friend Ranjana complaints that somebody has created a fake profile on Facebook and defaming her character with abusive comments and pictures. Identify the type of cybercrime for these situations.
Ans. Cyber Stalking
11 . In SQL, name the clause that is used to display the tuples in ascending order of an attribute.
Ans. ORDER BY
12 . In SQL, what is the use of IS NULL operator?
Ans. To check if the column has null value / no value
13 . Write any one aggregate function used in SQL.
Ans. SUM / AVG / COUNT / MAX / MIN
14 . Which of the following is a DDL command?
a) SELECT
b) ALTER
c) INSERT
d) UPDATE
Ans. b) ALTER
15 . Name The transmission media best suitable for connecting to hilly areas.
Ans. Microwave / Radio wave
16 . Identify the valid declaration of L:
L = [‘Mon’, ‘23’, ‘hello’, ’60.5’]
a. dictionary
b. string
c. tuple
d. list
Ans. d. List
17 . If the following code is executed, what will be the output of the following code?
name=”ComputerSciencewithPython”
print(name[3:10])
Ans. puterSc
18 . In SQL, write the query to display the list of tables stored in a database.
Ans. SHOW TABLES
19 . Write the expanded form of Wi-Fi.
Ans. Wireless Fidelity
20 . Which of the following types of table constraints will prevent the entry of duplicate rows?
a) Unique
b) Distinct
c) Primary Key
d) NULL
Ans. (c) Primary Key
21 . Rearrange the following terms in increasing order of data transfer rates.
Gbps, Mbps, Tbps, Kbps, bps
Ans. Bps, Kbps, Mbps, Gbps, Tbps
Section-II
Both the Case study based questions are compulsory. Attempt any 4
sub parts from each question. Each question carries 1 mark
22 . A departmental store MyStore is considering to maintain their inventory using SQL to store the data. As a database administer, Abhay has decided that :
• Name of the database – mystore
• Name of the table – STORE
• The attributes of STORE are as follows:
ItemNo – numeric
ItemName – character of size 20
Scode – numeric
Quantity – numeric
| ItemNo | ItemName | Scode | Quantity |
|---|---|---|---|
| 2005 | Sharpener Classic | 23 | 60 |
| 2003 | Ball Pen 0.25 | 22 | 50 |
| 2002 | Get Pen Premium | 21 | 150 |
| 2006 | Get Pen Classic | 21 | 250 |
| 2001 | Eraser Small | 22 | 220 |
| 2004 | Eraser Big | 22 | 110 |
| 2009 | Ball Pen 0.5 | 21 | 180 |
(a) Identify the attribute best suitable to be declared as a primary key
Ans. ItemNo
(b) Write the degree and cardinality of the table STORE.
Ans. Degree = 4 Cardinality = 7
(c) Insert the following data into the attributes ItemNo, ItemName and SCode respectively in the given table STORE.
ItemNo = 2010, ItemName = “Note Book” and Scode = 25
Ans. INSERT INTO store (ItemNo,ItemName,Scode) VALUES(2010, “Note Book”,25);
(d) Abhay want to remove the table STORE from the database MyStore. Which command will he use from the following:
a) DELETE FROM store;
b) DROP TABLE store;
c) DROP DATABASE mystore;
d) DELETE store FROM mystore;
Ans. (d) DROP TABLE store;
(e) Now Abhay wants to display the structure of the table STORE, i.e, name of the attributes and their respective data types that he has used in the table. Write the query to display the same
Ans. (e) Describe Store;
23 . Ranjan Kumar of class 12 is writing a program to create a CSV file “user.csv” which will contain user name and password for some entries. He has written the following code. As a programmer, help him to successfully execute the given task.
import _____________ # Line 1
def addCsvFile(UserName,PassWord): # to write / add data into the CSV file
f=open(' user.csv','________') # Line 2
newFileWriter = csv.writer(f)
newFileWriter.writerow([UserName,PassWord])
f.close()
#csv file reading code
def readCsvFile(): # to read data from CSV file
with open(' user.csv','r') as newFile:
newFileReader = csv._________(newFile) # Line 3
for row in newFileReader:
print (row[0],row[1])
newFile.______________ # Line 4
addCsvFile(“Arjun”,”123@456”)
addCsvFile(“Arunima”,”aru@nima”)
addCsvFile(“Frieda”,”myname@FRD”)
readCsvFile() #Line 5
(a) Name the module he should import in Line 1.
Ans. Line 1 : csv
(b) In which mode, Ranjan should open the file to add data into the file
Ans. Line 2 : a
(c) Fill in the blank in Line 3 to read the data from a csv file.
Ans. Line 3 : reader
(d) Fill in the blank in Line 4 to close the file.
Ans. Line 4 : close()
(e) Write the output he will obtain while executing Line 5.
Ans. Line 5 : Arjun 123@456
Arunima aru@nima
Frieda myname@FRD
Part – B
Section-I
24 . Evaluate the following expressions:
a) 6 * 3 + 4**2 // 5 – 8
b) 10 > 5 and 7 > 12 or not 18 > 3
Ans. a) 13
b) False
25 . Differentiate between Viruses and Worms in context of networking and data communication threats.
OR
Differentiate between Web server and web browser. Write any two popular web browsers
Ans. Viruses require an active host program or an already-infected and active operating system in order for viruses to run, cause damage and infect other executable files or documents Worms are stand-alone malicious programs that can self-replicate.
OR
Web Browser : A web browser is a software application for accessing information on the World Wide Web. When a user requests a web page from a particular website, the web browser retrieves the necessary content from a web server and then displays the page on the user’s device.
Web Server : A web server is a computer that runs websites. The basic objective of the web server is to store, process and deliver web pages to the users. This intercommunication is done using Hypertext Transfer Protocol (HTTP).
Popular web browsers : Google Chrome, Mozilla Firefox, Internet Explorer etc
26 . Expand the following terms:
a. SMTP
b. XML
c. LAN
d. IPR
Ans.
a. SMTP – Simple Mail Transfer Protocol
b. XML – eXtensible Markup Language
c. LAN – Local Area Network
d. IPR – Intellectual Property Rights
27 . Differentiate between actual parameter(s) and a formal parameter(s) with a suitable example for each.
OR
Explain the use of global key word used in a function with the help of a
suitable example.
Ans. The list of identifiers used in a function call is called actual parameter(s) whereas the list of parameters used in the function definition is called formal parameter(s).
Actual parameter may be value / variable or expression.
Formal parameter is an identifier.
Example:
def area(side): # line 1
return side*side;
print(area(5)) # line 2
In line 1, side is the formal parameter and in line 2, while invoking area() function, the value 5 is the actual parameter.
A formal parameter, i.e. a parameter, is in the function definition. An actual parameter, i.e. an argument, is in a function call.
OR
Use of global key word: In Python, global keyword allows the programmer to modify the variable outside the current scope. It is used to create a global variable and make changes to the variable in local context. A variable declared inside a function is by default local and a variable declared outside the function is global by default. The keyword global is written inside the function to use its global value. Outside the function, global keyword has no effect.
Example
c = 10 # global variable
def add():
global c
c = c + 2 # global value of c is incremented by 2
print(“Inside add():”, c)
add()
c=15
print(“In main:”, c)
output:
Inside add() : 12
In main: 15
28 . Rewrite the following code in Python after removing all syntax error(s). Underline each correction done in the code.
Value=30
for VAL in range(0,Value)
If val%4==0:
print (VAL*4)
Elseif val%5==0:
print (VAL+3)
else
print(VAL+10)
Ans. CORRECTED CODE:
Value=30
for VAL in range(0,Value) : # Error 1
if val%4==0: # Error 2
print (VAL*4)
elif val%5==0: # Error 3
print (VAL+3)
else: # Error 4
print(VAL+10)
29 . What possible outputs(s) are expected to be displayed on screen at the time of execution of the program from the following code? Also specify the maximum values that can be assigned to each of the variables Lower and Upper.
import random
AR=[20,30,40,50,60,70];
Lower =random.randint(1,3)
Upper =random.randint(2,4)
for K in range(Lower, Upper +1):
print (AR[K],end=”#“)
(i) 10#40#70#
(ii) 30#40#50#
(iii) 50#60#70#
(iv) 40#50#70#
Ans. OUTPUT: (ii)
Maximum value of Lower: 3
Maximum value of Upper: 4
30 . What do you understand by Candidate Keys in a table? Give a suitable example of Candidate Keys from a table containing some meaningful data.
Ans. A table may have more than one such attribute/group of attributes that identifies a tuple uniquely, all such attribute(s) are known as Candidate Keys.
table: Item
| Ino | Item | Qty |
|---|---|---|
| I01 | Pen | 500 |
| I02 | Pencil | 700 |
| I04 | CD | 500 |
| I09 | 700 | |
| I05 | Eraser | 300 |
| I03 | Duster | 200 |
In the above table Item, ItemNo can be a candidate key
31 . Differentiate between fetchone() and fetchall() methods with suitable examples for each.
Ans. fetchall() fetches all the rows of a query result. An empty list is returned if there is no record to fetch the cursor.
fetchone() method returns one row or a single record at a time. It will return None if no more rows / records are available.
32 . Write the full forms of DDL and DML. Write any two commands of DML in SQL.
Ans. DDL – Data Definition Language
DML – Data Manipulation Language
Any two out of INSERT, DELETE, UPDATE
33 . Find and write the output of the following Python code:
def Display(str):
m=""
for i in range(0,len(str)):
if(str[i].isupper()):
m=m+str[i].lower()
elif str[i].islower():
m=m+str[i].upper()
else:
if i%2==0:
m=m+str[i-1]
else:
m=m+"#"
print(m)
Display('Fun@Python3.0')
Ans. OUTPUT : fUNnpYTHON
Section- II
34 . Write a function LShift(Arr,n) in Python, which accepts a list Arr of numbers and n is a numeric value by which all elements of the list are shifted to left. Sample Input Data of the list
Arr= [ 10,20,30,40,12,11], n=2
Output
Arr = [30,40,12,11,10,20]
Ans.
def LShift(Arr,n):
L=len(Arr)
for x in range(0,n):
y=Arr[0]
for i in range(0,L-1):
Arr[i]=Arr[i+1]
Arr[L-1]=y
print(Arr)
35 . Write a function in Python that counts the number of “Me” or “My” words present in a text file “STORY.TXT”.
If the “STORY.TXT” contents are as follows:
My first book
was Me and
My Family. It
gave me
chance to be
Known to the
world
The output of the function should be:
Count of Me/My in file: 4
OR
Write a function AMCount() in Python, which should read each character of a text file STORY.TXT, should count and display the occurance of alphabets A and M (including small cases a and m too).
Example:
If the file content is as follows:
Updated information
As simplified by official websites.
The EUCount() function should display the output as:
A or a:4
M or m :2
Ans.
def displayMeMy():
num=0
f=open("story.txt","rt")
N=f.read()
M=N.split()
for x in M:
if x=="Me" or x== "My":
print(x)
num=num+1
f.close()
print("Count of Me/My in file:",num)
OR
def count_A_M():
f=open("story.txt","r")
A,M=0,0
r=f.read()
for x in r:
if x[0]=="A" or x[0]=="a" :
A=A+1
elif x[0]=="M" or x[0]=="m":
M=M+1
f.close()
print("A or a: ",A)
print("M or m: ",M)
36 . Write the outputs of the SQL queries (i) to (iii) based on the relations Teacher and Posting given below:
| T_ID | Name | Age | Department | Date_of_join | Salary | Gender |
|---|---|---|---|---|---|---|
| 1 | Jugal | 34 | Computer Sc | 10/01/2017 | 12000 | M |
| 2 | Sharmila | 31 | History | 24/03/2008 | 20000 | F |
| 3 | Sandeep | 32 | Mathematics | 12/12/2016 | 30000 | M |
| 4 | Sangeeta | 35 | History | 01/07/2015 | 40000 | F |
| 5 | Rakesh | 42 | Mathematics | 05/09/2007 | 25000 | M |
| 6 | Shyam | 50 | History | 27/06/2008 | 30000 | M |
| 7 | Shiv Om | 44 | Computer Sc | 25/02/2017 | 21000 | M |
| 8 | Shalakha | 33 | Mathematics | 31/07/2018 | 20000 | F |
| P_ID | Department | Place |
|---|---|---|
| 1 | History | Agra |
| 2 | Mathematics | Raipur |
| 3 | Computer Science | Delhi |
i . SELECT Department, count(*) FROM Teacher GROUP BY Department;
ii . SELECT Max(Date_of_Join),Min(Date_of_Join) FROM Teacher;
iii . SELECT Teacher.name,Teacher.Department, Posting.Place FROM Teachr, Posting WHERE Teacher.Department = Posting.Department AND Posting.Place=”Delhi”;
Ans. OUTPUT:
i.
| Department | Count(*) |
|---|---|
| History | 3 |
| Computer Sc | 2 |
| Mathematics | 3 |
ii . Max – 31/07/2018 or 2018-07-31 Min- 05/09/2007 or 2007-09-05
iii .
| name | Department | Place |
|---|---|---|
| Jugal | Computer Sc | Delhi |
| Shiv Om | Computer Sc | Delhi |
37 . Write a function in Python PUSH(Arr), where Arr is a list of numbers. From this list push all numbers divisible by 5 into a stack implemented by using a list. Display the stack if it has at least one element, otherwise display appropriate error message.
OR
Write a function in Python POP(Arr), where Arr is a stack implemented by a list of numbers. The function returns the value deleted from the stack.
Ans.
def PUSH(Arr,value):
s=[]
for x in range(0,len(Arr)):
if Arr[x]%5==0:
s.append(Arr[x])
if len(s)==0:
print("Empty Stack")
else:
print(s)
OR
def popStack(st) :
# If stack is empty
if len(st)==0:
print("Underflow")
else:
L = len(st)
val=st[L-1]
print(val)
st.pop(L-1)
38 . MyPace University is setting up its academic blocks at Naya Raipur and is planning to set up a network. The University has 3 academic blocks and one Human Resource Center as shown in the diagram below

Center to Center distances between various blocks/center is as follows:
| Law Block to business Block | 40m |
|---|---|
| Law block to Technology Block | 80m |
| Law Block to HR center | 105m |
| Business Block to technology Block | 30m |
| Business Block to HR Center | 35m |
| Technology block to HR center | 15m |
Number of computers in each of the blocks/Center is as follows:
| Law Block | 15 |
| Technology Block | 40 |
| HR center | 115 |
| Business Block | 25 |
a) Suggest the most suitable place (i.e., Block/Center) to install the server of this University with a suitable reason.
b) Suggest an ideal layout for connecting these blocks/centers for a wired connectivity.
c) Which device will you suggest to be placed/installed in each of these blocks/centers to efficiently connect all the computers within these blocks/centers.
d) Suggest the placement of a Repeater in the network with justification.
e) The university is planning to connect its admission office in Delhi, which is more than 1250km from university. Which type of network out of LAN, MAN, or WAN will be formed? Justify your answer.
Ans.
a. Most suitable place to install the server is HR center, as this center has maximum
number of computers.
b .
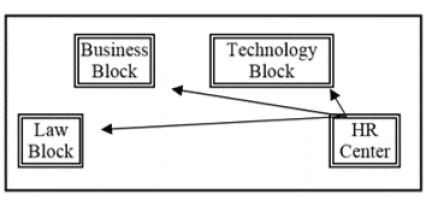
c. Switch
d. Repeater may be placed when the distance between 2 buildings is more than 70
meter.
e. WAN, as the given distance is more than the range of LAN and MAN
39 . Write SQL commands for the following queries (i) to (v) based on the relations Teacher and Posting given below:
| T_ID | Name | Age | Department | Date_of_join | Salary | Gender |
|---|---|---|---|---|---|---|
| 1 | Jugal | 34 | Computer Sc | 10/01/2017 | 12000 | M |
| 2 | Sharmila | 31 | History | 24/03/2008 | 20000 | F |
| 3 | Sandeep | 32 | Mathematics | 12/12/2016 | 30000 | M |
| 4 | Sangeeta | 35 | History | 01/07/2015 | 40000 | F |
| 5 | Rakesh | 42 | Mathematics | 05/09/2007 | 25000 | M |
| 6 | Shyam | 50 | History | 27/06/2008 | 30000 | M |
| 7 | Shiv Om | 44 | Computer Sc | 25/02/2017 | 21000 | M |
| 8 | Shalakha | 33 | Mathematics | 31/07/2018 | 20000 | F |
| P_ID | Department | Place |
|---|---|---|
| 1 | History | Agra |
| 2 | Mathematics | Raipur |
| 3 | Computer Science | Delhi |
i. To show all information about the teacher of History department.
ii. To list the names of female teachers who are in Mathematics department.
iii. To list the names of all teachers with their date of joining in ascending order.
iv. To display teacher’s name, salary, age for male teachers only.
v. To display name, bonus for each teacher where bonus is 10% of salary.
Ans.
i. SELECT * FROM teacher WHERE department= “History”;
ii. SELECT name FROM teacher WHERE department= “Mathematics” AND
gender= “F”;
iii. SELECT name FROM teacher ORDER BY date_of_join;
iv. SELECT name, salary, age FROM teacher WHERE gender=’M’;
v. SELECT name, salary*0.1 AS Bonus FROM teacher;
40 . A binary file “Book.dat” has structure [BookNo, Book_Name, Author, Price].
i. Write a user defined function CreateFile() to input data for a record and add to Book.dat .
ii. Write a function CountRec(Author) in Python which accepts the Author name as parameter and count and return number of books by the given Author are stored in the binary file “Book.dat”
OR
A binary file “STUDENT.DAT” has structure (admission_number, Name, Percentage). Write a function countrec() in Python that would read contents of the file “STUDENT.DAT” and display the details of those students whose percentage is above 75. Also display number of students scoring above 75%
Ans.
import pickle
def createFile():
fobj=open("Book.dat","ab")
BookNo=int(input("Book Number : "))
Book_name=input("Name :")
Author = input(“Author: “)
Price = int(input("Price : "))
rec=[BookNo,Book_Name,Author,Price]
pickle.dump(rec,fobj)
fobj.close()
def CountRec(Author):
fobj=open("Book.dat","rb")
num = 0
try:
while True:
rec=pickle.load(fobj)
if Author==rec[2]:
num = num + 1
except:
fobj.close()
return num
OR
import pickle
def CountRec():
fobj=open("STUDENT.DAT","rb")
num = 0
try:
while True:
rec=pickle.load(fobj)
if rec[2] > 75:
print(rec[0],rec[1],rec[2],sep="\t")
num = num + 1
except:
fobj.close()
return num

